A New Way to Fight Retail Shrink & Protect Profits
Retail shrinkage is a serious concern for today’s businesses. Strictly defined, it’s inventory loss due to shoplifting, employee theft, administrative mistakes, or fraud by your suppliers. It’s a significant burden on hardworking business owners and retail organisations in Australia and around the world.
The problem is one that’s also been growing over time. The National Retail Association of Australia claims that shoplifting, robbery, and vandalism cost the country’s businesses up to $9 billion in a typical year — and that’s without factoring in the impact that the pandemic has had on retail theft as times grow more difficult.
As a security company with decades of experience, we know firsthand the dire importance of combating retail shrink. This article will take a closer look at the problem, examine some of its more common causes, and discuss a proven framework for navigating it with seasoned professionals’ help.
A Closer Look at Retail Shrink
Retail shrink is an easy problem to over-simplify. Often, people reduce it to a dichotomy of, We’ve been robbed! Or, Somebody messed up! In reality, appreciating its complexity can be a big help for businesses looking to address it. This first section will take a closer look at the causes of shrinkage.
Retail Shrink Due to Shoplifting
There’s an all-too-common misconception that the average retailer must factor theft into its financial and resource planning. Somehow, it’s become a de-facto rule of retail trade that a business will lose goods to theft and therefore learn to expect it.
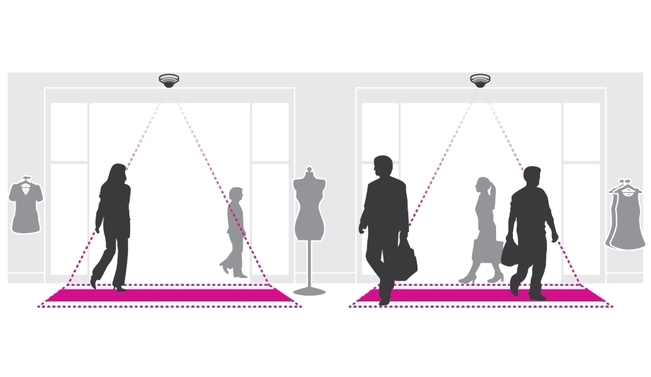
The fact of the matter is that shoplifting is greatly preventable, and by no means a given. It often boils down to failures to deter and detect. Deterrents like visible on-premise cameras, point of sale (POS) integration, video analytics enforcing the correct usage of store entries and exits (using direction of travel analytics), and embedded technology (ex. RFID chips) for big-ticket items can discourage would-be thieves from victimising your business. Likewise, there are measures you could employ to detect shoplifters in the act and catch them before it’s too late—we’ll be discussing these later on.
Retail Shrink Due to Employee Theft
Employee theft is probably the worst and most difficult cause of retail shrink that your business will have to manage. Your staff have the benefit of knowing your store’s layout and protocols, as well as an idea of how to expect their colleagues to behave. Worse yet, they’re more likely to be aware of gaps in your security. Knowing when new inventory is unattended or the blind spots you have in your camera setup, can lead to temptation. But this can be overcome using tools like integrated video surveillance and access control so that access to high value items is highly restricted – and recorded – or by using a custom object detection analytic that lets you know when an object has been removed from a scene. Additionally, you can prevent camera tampering using a camera integrity monitoring application – such as the Camera Integrity Monitor in Genetec Security Center – which automatically identifies cameras that could have been obscured or tampered with.
As with shoplifting, preventing employee theft is a matter of deterrence and detection. Controlling information and having multiple layers to your security protocols is one necessary step, as is a set of rules for accountability.
Retail Shrink Due to Clerical Errors
Human error is unavoidable. The people who operate your store are imperfect beings, and incidents like counting mistakes and lost or forgotten inventory is likely to happen. Per Statista, this accounts for around 19% of retail shrinkage in the United States — and we don’t expect a big difference in proportion in Australia.
Retail Shrink Due to Vendor Fraud
In some cases, your suppliers may be responsible for your inventory shrinkage. By accident or by design, your vendors may be delivering fewer goods than promised or fudging the numbers on their invoices. Where this form of shrinkage is concerned, extra mindfulness and precise accounting will go a long way towards reducing the harm to your business.
The Framework: Professional Security for Shrinkage Prevention
After decades of experience servicing customers in the retail industry, we’ve identified three key layers to private security that can help minimise inventory shrinkage. While the security industry and its stakeholders are continually evolving, we find that the following framework for understanding security plays a vital role in protecting our customers’ businesses.
Consider the following as components of a bigger picture. While each item on our list provides significant benefits on their own, they come together to form a mesh of defensive measures.
The Digital Layer
There’s a good reason why surveillance equipment is the first thing that comes to mind when most people think of retail security. The earliest camera deployments were revolutionary: they allowed retailers to see everything in real-time and step backwards in time to investigate losses.
Today’s surveillance systems have changed the game yet again. Beyond obvious improvements to video quality, loss prevention investigators can search POS to camera integrations for suspicious transaction behavior and immediately view the corresponding video, like refund transactions that have taken place in the last week where there is no motion detected on the customer side of the register or filter POS transactions by various criteria such as type and amount or for all transactions in the last 24hrs above $100. Additionally, if sales of mens rasors aren’t adding up, with the POS data and stock not matching, then a loss prevention team member can pull the video straight up to ascertain if customers are surreptitiously hiding the number of rasors that they’re buying or the staff are miscounting and not charging for all of the goods purchased. Genetec’s Security Center Transaction Finder application matches point-of-sale transactions with video of every transaction.
The latest video surveillance software applications provide connections for mobile phones and web clients through internet connections — allowing for monitoring to occur away from a central control room – helping retail loss prevention teams speed up
investigations across one store or many.
It’s an investment to be sure, but one that can be backed by numbers: the manufacturers behind these surveillance systems have seen shrinkage reductions of up to 30% from the moment of installation.
The Policy Layer
Preparation is key when it comes to incident prevention, and a retailer’s efforts to address shrinkage should aim to solve these problems before they begin. In our experience, incident prevention is a matter of creating smart policies that get ahead of retail shrink causes.
As we’ve mentioned, there are multiple ways to deter shoplifters. On top of what’s been said, we find that larger establishments benefit from more calculated staff deployment systems: devising ways to deploy your staff so that you reduce the amount of time that your patrons and guests spend unattended.
The policy layer shines when addressing staff-related shrinkage, especially if you adopt the zero-trust paradigm more commonly encountered in reference to cyber security. It’s the in-thing when it comes to access management, and it centres on the idea of creating trust as a source of vulnerability.
We’ve found that zero-trust lends itself very well to the physical side of the security equation. We prefer to implement layered plans and protocols to control how much our clients’ employees know at a time. For example, employee schedules can be set to rotate, with information about who gets staffed where and when dispensed on a need-to-know basis.
Likewise, we believe in careful monitoring and control of our clients’ access points. Maintaining a stringent, digitised record of who accesses areas containing sensitive information and goods is a strong deterrent against internal theft—when people have no way of masking where they’ve been (and when), they’ll be less likely to risk being discovered.
It pays to remove temptation and limit options for theft. Any framework for reducing retail shrinkage should recognise that trust makes you vulnerable, and keep eyes on your critical areas at all times.
The Workflow Design Layer
Workflow design can spell the difference between success and failure in security. All the cameras, guards, and rules in the world won’t mean a thing if your daily routines come with glaring vulnerabilities.
When re-examining your security, pay attention to how your employees have been instructed to go about their tasks. You’re more likely than not to find processes and tasks that leave areas unobserved, or otherwise lend advantages to would-be thieves. Such reviews benefit from security professionals’ experience and perspective, who may be in a better position to spot flaws in your process design.
Not every aspect of your workflow can be controlled, of course. Any processes that, by nature, require a high degree of trust can be secured at the digital layer: cameras, access monitoring, software, and other tech-based solutions can cover what workflow design cannot.
Conclusion
The best security professionals take a holistic approach to security. They must be able to think from multiple perspectives: that of their clients, that of their clients’ guests and customers, and that of criminals.
At JD security, we focus on attaining skills, talent, and perspectives that allow us to address industry-specific concerns, and retail shrink is no exception. As a leading company in the private security space, we’ve refined a system that allows us to address the challenges of retail security with focus and painstaking attention to the inner workings of retail trade.
Consult with our experts today to learn how we can lend our expertise towards reducing your inventory losses and maximising your operational security.
Call us on 1300 556 334 or email [email protected] to learn more.
Customers in New Zealand call 0800 345 677 or email [email protected].
Latest Posts
Comments are closed.