Security Systems
Security System Installation, Maintenance & Support
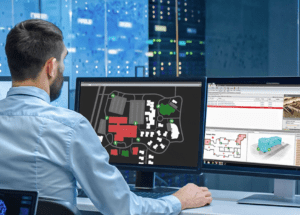
JD Security has been a professional, innovative security systems integrator for over four decades. We are dedicated to being a trusted partner and consistently provide exceptional value through collaborative solutions tailored to our customer’s unique needs.
Learn More about Business Security Systems
Business Security Systems for Diverse Industries
JD Security designs, installs, and services physical security systems across multiple industries, including Retail, Education, Commercial Property, Healthcare, Distribution & Logistics, Industrial Facilities, Hospitality, and Pharmaceuticals. This comprehensive approach ensures that all aspects of physical security are covered, providing high protection for people, property, assets and business operations.
Key Features of a Security System
The essential features outlined in the following recommendations are crucial factors when selecting a new system.
- Intrusion Detection: detects and alerts responsible parties about potential security breaches or threats. Compatible detection devices include motion detectors, door/window contacts, or glass break detectors to detect unauthorised entry into protected areas.
- Fire & Smoke Detection: security systems often integrate fire and smoke detectors to detect the presence of fire or smoke within a facility. When smoke or heat is detected, an alarm is activated to notify occupants and initiate emergency protocols.
- Panic & Duress Alarms: these are designed to be activated discreetly in emergencies where individuals feel threatened or distressed. Panic buttons or special codes can trigger these alarms, alerting security personnel or authorities to the situation.
- Partitioning: A security system’s partitioning function divides the system into separate sections, enabling independent management and custom security settings for different areas or user groups. This feature allows for specific codes to control access to each partition, ensuring only authorized users can manage the security settings for their respective areas.
- Integrated Access Control: it enables seamless control and management of access to secure areas within a facility.
- Management Software offers advanced integration with other systems, including CCTV, fire systems, lifts, lighting control, and third-party access control systems. It also supports automation.
- Web Client: A web client lets users access the system from anywhere using a web browser. This means they do not need extra software.
- Reporting: The system software should create standard reports. These include Users Arming & Disarming, Users Time-on-Site, and Muster Reports. Muster Reports indicate which users are present in any section at the time of the report.
Entrance and Exit readers are utilised to create this report. User Access History and many more. For the technically minded, these sample reports can be used as templates to customise and generate other reports according to the customer’s needs.
- Enterprise Mobility: an iOS or Android app to control the system, including arming and disarming, remote control of doors, inputs, auxiliaries, viewing system event logs, and more.
- Scalability: the system should be deployable across multiple sites and locations. This distributed architecture promotes scalability by allowing the system to expand effortlessly across different areas or buildings while retaining centralised control.
- Communications: 4G/5G, LAN, TCP/IP (Ethernet), email, SMS, fiber optic and Wi-Fi.
- Active Directory Integration: Azure Active Directory is already used as the main user management database, integrating many other business systems (Email, Payroll, Scheduling, etc.). Integrity can also leverage this centralised source of user data, delivering great cost-efficiencies to the organisation by negating the need for additional user data entry. Integriti operator training time is also significantly reduced.
- Automatic Number Plate Recognition (ANPR): helps manage parking efficiently. It allows you to search for a vehicle using its license plate. It also keeps unwanted vehicles out of a car park.
- BMS: Inner Range Integriti can directly control many third-party systems like elevators, heating, cooling, and lights. It can also communicate with Building Management Systems. This allows it to be a key part of any smart building solution.
- Biometrics: Biometric Access Control technology provides an increased level of security for building access control systems when compared to traditional card & card reader technologies. Integriti’s integrated platform facilitates a streamlined on-boarding process when integrated with third-party Biometric Access Control modules. The synchronization of users ultimately simplifies the on-boarding process, increasing System Operator’s overall efficiency.
- Intercoms: Security & Access Control systems are often installed in conjunction with Intercom systems; as such, it’s of paramount importance that these systems are able to operate together.
- Lockers: Utilising a synchronised user database, Integriti’s integrated platform facilitates seamless user management for Locker systems. User information can be solely managed from Integriti, meaning that System Operators do not need to maintain two separate databases. Additionally, Integriti’s powerful reporting tools can be utilised to develop reports specifically related to Locker events, giving system owners full awareness of which users have accessed which lockers and when.
- Wireless Access Control: By integrating a Wireless Access Control system with Integriti, system operators do not need to manage multiple user databases. Synchronisation of users and access permissions allows Integriti to be the single interface for managing Wireless Access Control doors – mitigating the requirement to manage multiple platforms.
- SMS: Integriti’s powerful communications capabilities allow for SMS sending from within the Integriti Software. Messages can be sent to any user or group of users, and can be sent on demand or via a range of different variables (e.g. time schedules). SMS sending can be incredibly powerful in situations where it is critical to notify all users on-site of emergency situations such as a fire drill, lockdown, or active shooter.
- RTLS: Real-Time Location Systems are commonly deployed in high security situations, and allow Security Operators to maintain accurate status and location of Security Personnel in real-time. The RTLS integration with Integriti allows for status updates and location monitoring via the same graphical interface as every other aspect of the Integriti system (including integrated CCTV, Intercoms, etc.). While increasing security and safety of staff, this integration improves situational awareness of Security Personnel in high security situations.
- Hardware Acquisition Costs: This includes access control panels, door controllers, keypads, readers, sensors, and auxiliary devices such as power supplies and backup units.
- Software Licensing Costs: One-time or perpetual license fees for management software, which may vary depending on the number of access points, users, and specific software modules.
- Installation Costs: Labor costs associated with installing system hardware, including:
- Running cables for access control points, readers, and other peripherals.
- Alarm Systems: PIR Motion Sensors, Door Sensors & Smoke Detectors, Duress Alarms, Panic Alarms, Alarm Panel is hard-wired so the power can’t be cut, Back-Up Battery in case of a power outage – no integration with 3rd party systems.
- Combined Access Control & Intruder Detection Systems: provide integration to other systems, including Access Control, CCTV, and Video Surveillance Systems.
- Integrated Security Systems: include an Access Control System, mobile access control credentials, video management systems, visitor management, lighting control, dual-factor authentication, facial recognition, mobile apps, intercoms, biometrics & lift systems.
- We ensure that your alarm system is professionally installed in accordance with best practice & delivered on time
- ISO 9001:2015 certified for Quality Management, 45001:2018 Occupational Health & Safety and 14001:2015 Environmental Management
- Our in-house Grade A1 Security & Video Monitoring Centre – no third party Monitoring Centres used – is AS/NZS 2201.2-2004 certified & provides you with greater monitoring accuracy, than using a third party provider and custom automation abilities
- 4G Security Monitoring from your platform of choice – Inner Range Multipath, DirectWireless, Permaconn or Telstra Secure
What are the Advanced Features of a Security System that I should consider?
Understanding the Total Cost of Ownership of a Physical Security System
The Total Cost of Ownership (TCO) for a physical security system includes various cost elements beyond the initial purchase. Below is a breakdown of the key components that comprise the TCO.
Capital Expenditure (CapEx)
Installation
Business Systems are designed and installed by our in-house engineering team and delivered by a dedicated Project Manager, who oversees the team installing your security system. Our teams include qualified and manufacturer certified technicians. We also provide on-site service, maintenance plans & premium remote support.
Maintenance and Support
We provide on-site service, maintenance plans, and remote support to keep your security systems operating at peak performance.
Overnight service requests are booked through our Monitoring Centre and are available for our Service Team the next business day.
Expert Advice
With more than 40 years of experience and over 10,000 business security systems installed, we are the experts you can trust. Our expertise includes:
Dedicated Service Team
Our service team is available for booking service requests from Monday to Friday, 9:00 AM to 5:00 PM. Overnight service requests are booked through our Monitoring Centre and are available for our Service Team the next business day.
We also have dedicated national remote support engineers who provide our project and service teams and customers fast support when required. Emergency service requests (i.e. overnight & public holidays) are co-ordinated by our Grade A1 Monitoring Centre.
Standards & Compliance
We’re dedicated to quality:
Contact Us
Call us on 1300 556 334 or email [email protected] to learn more.
Customers in New Zealand call 0800 345 677 or email [email protected].