Minimise contact, improve efficiency & reduce costs with HID Mobile Access
Mobile phones are a pivotal part of today’s technological landscape, in and out of business. Gone are the days where we needed to log onto a computer to access emails and documents — your entire work life now resides on your handheld device.
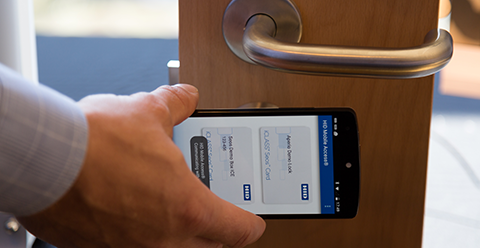
Moving with this trend, HID Global has taken the utility of mobile phones a step further through HID Mobile Access. HID Mobile Access is HID’s unique technology that replaces older access control credentials, such as key fobs and proximity cards, with a mobile app that integrates access to doors, networks, and more.
In this article, we’ll take a closer look at HID Mobile Access’s features and how this solution can work for your business.
How HID Mobile Access works
Providing secure access to stakeholders in and out of the organisation is made simple through Mobile Access. The administrator sets up the user in HID Origo — Mobile Access’ cloud-based management portal—which automatically sends an email to the user with a link and invitation code to download the mobile app. Once the user registers, they’re issued a mobile credential.
The Mobile Access app is flexible, and can store multiple credentials or authorisations for different access points from foreign issuers, e.g. access to doors in various departments in a building. The app will automatically identify which certification is required for the access point. These credentials are user-based rather than device-based, staying true to its promise of providing all-in-one access through a mobile phone.
Benefits of HID Mobile Access
Universal Compatibility
The HID Mobile Access app is compatible with iOS & Android mobile phones, tablets & wearables including the Apple Watch. Depending on the user’s device, the app can operate via BLE (Bluetooth Low Energy) or NFC (Near Field Communication) to connect the device to access points wirelessly.
For a complete list of HID Mobile Access supported devices with their corresponding reliability rating, visit the HID website.
Mobile Access’ compatibility with a wide range of devices means that organisations don’t have to provision new credentials for employees or guests — they can utilise what people already have powered by a single application.
Multi-functionality
We’ve mentioned doors and networks, but Mobile Access offers much more. It can be linked with almost anything that may needs a security layer, e.g. printers, computers, and other machines. With its ability to store information, employers can also easily access attendance and movement data within the office.
Security
A key concern for security systems is identity protection, a need anticipated by HID by integrating their iClass SE Readers with Mobile Access. iClass SE Readers have multi-layered security that ensures authentication through its Secure Identity Object (SIO). SIO is HID’s data model that transmits encrypted identity information to prevent unauthorised access to touchpoints and networks. iClass SE Readers also have EAL5+ (Evaluation Assurance Level) Certified Secure Level Hardware, which assures that the data transmitted in the system are secure.
Scalability
HID doesn’t expect your business (or your budget) to stay the same. Their subscription model allows for flexibility to add or remove user licenses depending on your current needs.
How HID Mobile Access helps businesses during the pandemic
With the current COVID-19 situation, we’re all focused on minimising contact. Mobile Access allows businesses to comply with this in several ways.
Remote User Enrolment
Mobile credentials generated by the system can be provided to users without face-to-face interaction with administrators. With older credential technologies, such as swipe cards , an issuer needs to touch the card, swipe it through a card reader, and hand over the card to the user. Considering the frequency and speed this process is done, there’s a high possibility that devices and cards used won’t be adequately sanitised. The use of mobile access removes this risk.
Location Data
With real-time location (RTL) and proximity-based location services, employers can easily monitor employee performance without coming into close contact with them. Having Mobile Access strikes a balance between monitoring performance KPIs, and compliance with safety measures.
Unlocking doors from a distance
Mobile Access allows a user to open doors in three ways:
- Short range tap
- Twist & Go (twist and go motion of the device from a distance)
- App Specific (e.g. using a widget from an Apple Watch)
The latter two are unique no contact solutions provided by Mobile Access, eliminating contact between two surfaces (phone & reader). These solutions also eliminate the risk of contracting the virus from insufficient or incomplete sanitation of surfaces. Furthermore, having these options to open doors ensures that people can enter and exit locations faster without creating traffic.
Conclusion
The functionality of mobile phones (and wearables) has expanded from secure sign-on to tools improving access to what once wasn’t considered possible. Coupled with HID’s technology and ecosystem, they’re now, more than ever, also critical in managing employees’ health and safety.
Call us on 1300 556 334 or email [email protected] to learn more.
Customers in New Zealand call 0800 345 677 or email [email protected].
Latest Posts
Comments are closed.